Technology is always evolving and shaping up the future of business strategies. Organizations continually try to adopt new technologies to overhaul their business infrastructure and keep up with the pace of changing market dynamics. Leveraging the benefits of AI for process automation has been implemented by several businesses. But, it is still not enough, and there is a lot more to AI that will form the crux of technology disruption in the coming years.
Here is a list of significant technology disruption that is all set to mark a new territory of innovation in the coming five years:
1. Artificial intelligence:
The growth of artificial intelligence in the technology sector has been remarkable, and there have been no signs of its slowing down. In the next five years, we can expect that they will play a significant role in transforming the workplace environment and replacing manual labor. The technology disruption with AI will result in a loss of human jobs at a massive rate as companies tend to prefer economic and efficient systems. The best example of this is the chatbots (chat+robot) that are simulated using natural language processing and artificial intelligence that provide enhanced operational efficiency, 24*7 service and no demands of any working conditions.
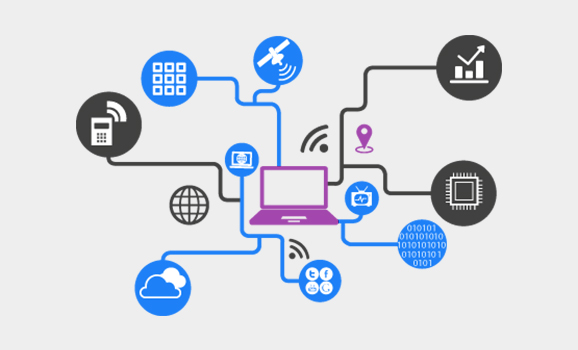
2. Insurtech:
The automation in the Insurance sector is gaining momentum currently. For the past few years, the insurance sector was hardly on the map of technology innovation. But, as the technology is getting intertwined in the everyday lives of the people Insurance companies have started adopting technology innovation at a rapid rate. Some of these innovations include Insurance chatbots which are available at all the times to provide solutions to their customers, automated system to perform the internal processes and redundant tasks, AI-based insurance software that processes the claims and service requests quickly.
3. RPA(Robotic process automation):
RPA is the next big thing that will lead to major technology disruption in the coming years. It has already made its way in most of the technology companies, and RPA for insurance is also gaining popularity. With the passage of time, it will just become more advanced and smart replacing a good chunk of human-operated operations. RPA has branched out from three key technologies, i.e., screen scraping, workflow automation and artificial intelligence making it capable of automating business processes and improving the overall work efficiency.
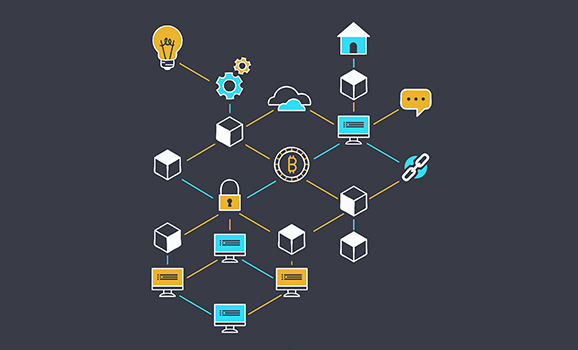
4. Blockchain:
Cryptocurrency based blockchain is the next disrupting technology that has already changed the conventional model of trading and business transaction. Blockchain forms the backbone of cryptocurrencies and Bitcoins. The prominence of Blockchain in the next five years is set to increase by leaps and bounds and will mainstream the payment methods by 2020. Blockchain works on the concept of decentralization where duplicate copies of each ledger are stored on various locations, so there is no focal point of vulnerability that can be exploited by the hackers. It makes blockchain a secure platform altogether. The overall cost of implementing blockchain is quite less because there are no additional costs related to the third parties and is also free from human intervention.
4 Things That Made Blockchain The Most Disruptive Tech In Decades
6. Augmented Reality (AR) & Virtual Reality (VR):
As of now, augmented and virtual reality’s existence is limited to the entertainment and gaming industry. But, the future prediction depicts that in the coming years AR will play a significant role in other sectors as well. It will not be surprising to see advancements in AR/VR technology in the healthcare, e-commerce and travel industry.
The above mentioned list was our round-up of the major technology disruption that will happen in the next five years. Though the list can go on and on and you can always find something new to add to the list.
Knowledge thats worth delivered in your inbox