The earliest known reason for introducing insurance protection in Kenya, came during the time of the Colonial British — when they insured their farms and crops against loss, damage etc. Today, Kenya has 70% of the East African Insurance market (among Burundi, Uganda, Tanzania & Rwanda). Still, African Insurance is relatively nascent in terms of size. Only 6 major markets dominate the landscape in a serious way — Egypt, Tunisia, Morocco, South Africa, Nigeria & Kenya. Infact, the number of insurtech startups in the continent altogether is a paltry 50 something.
The looming political climate coupled with a slowly recovering economy and some fierce competitive tactics used by traditional incumbents places the industry far from ideal in terms of marketplace conditions, including the slowdown in uptake of insurance products by an income-sensitive population.
Yet, Kenya offers a sense of growing appeal for young insurtechs in this region. The market remains largely undisrupted, since insurance penetration is only about 3% (insurance penetration for the African continent is only at 0.3%), attracting large international insurers like Allianz and Swiss Re who have recently entered the market. Kenya, like other countries in the region, has enormous potential similar to South-East Asian economies that also remain largely undisrupted with lower penetration rates.
The positive sentiment surrounding Kenya’s potential for deep tech disruption is not surprising — According to the 2019 Government AI Readiness Index published by the IDRC and Oxford Insights — Kenya is the most AI ready country in Africa.
Buying Behavior
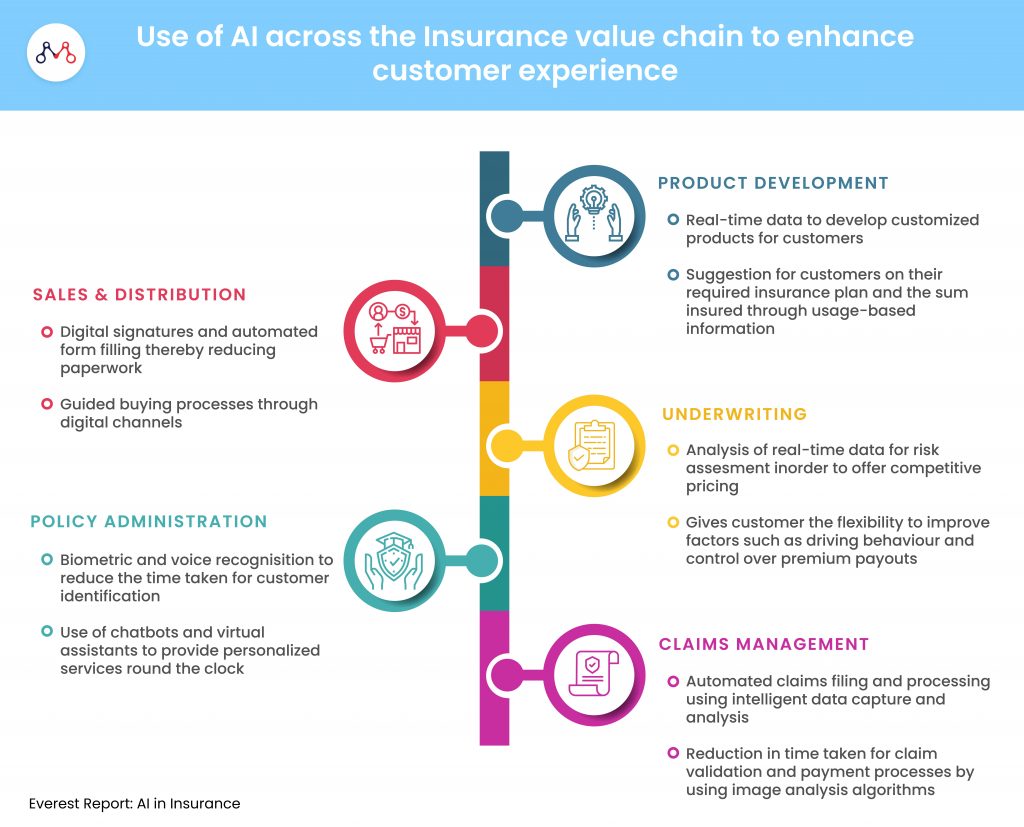
Insurtech startups are exploring avenues using AI that large, traditional players have less incentive to exploit, such as offering ultra-customized policies, social insurance, and using behavior data from devices to dynamically price premiums.
The Millennial experience is entirely technology driven, while their attitudes and perceptions as consumers will shape the future of how insurance as a service continues to remain relevant.
According to a Kenya Insurance Industry Report, 65% of millennials compare prices across different websites before making a purchase, 68% only buy a product through referrals from friends and social media. Interestingly, 84% of them are opposed to traditional advertising.
For insurers, loyalty comes at a price — often dictated by the pain point the product/service can eliminate for impatient classes of customers. Analysing buying or browsing behavior can lead to an immense amount of ethically siphoned data. Using ML models and regression algorithms, insurers can create a unified view of their prospect, and realize a multi-targeted approach to create opportunities for upselling or cross-selling.
The report also highlights the importance of making sense of social media behavior — since 41% of millennials use social networking sites to pass on recommendations of products and services to friends and family.
Unlocking market potential requires targeting the uninsured growing middle class in creative ways. In addition to better pricing models, insurtech startups are testing the waters on a host of potential game-changers, such as using deep learning trained artificial intelligence (AI) to handle the tasks of brokers and finding the right mix of policies to complete an individual’s coverage.
Insurtechs are using AI to solve for Kenya’s distribution challenges, by looking at vital consumer needs that have previously been unmet or glossed over. At the same time, there is scope for improving the average consumer’s awareness of artificial intelligence technology, and how they can take advantage of it to solve priority-first issues related to convenience, cost and range of choice.
Nairobi-based Jubilee Insurance, the largest insurer in East Africa is making the most of AI tools like chatbots and automated messaging platforms for streamlining simple customer feedback & support operations. They have also launched forward-thinking products like “Recover in Style” which provides hair and make-up services to Jubilee patients who are hospitalized — services that go beyond the financial needs and into the realm of delivering superior customer experiences.
These efforts highlight a trend pointing towards the growing interest in the use of apps to pull policies into one platform for management and monitoring, creating on-demand insurance for micro-events like borrowing a friend’s car, and the adoption of the peer-to-peer models to create customized coverages. Bluewave, for example, is an insurtech startup offering low-cost insurance products, as low as US$4 a week, aimed at low-resource, low-income users in last-mile environments.
The expanding middle class and growth in mobile phone penetrations will be critical to widening distribution and getting more people to buy micro-insurance sized products for the first time. Badalaa is an on-demand insurtech startup focussed on bringing insurance at the point of transaction where the user needs it. Turaco, a recently funded insurtech, with premiums for as little as US$2 — leverages mobile financial services to provide hospital cashback to customers who have sought treatment at any nationally-accredited hospital in the regions where they operate. These innovations further the consumer’s awareness of AI-enabled insurance coverage and protection in general, in an otherwise underpenetrated marketplace.
Bismart is another example — an insurtech aggregator that allows customers to not only buy the best-in-class insurance products but also make claims directly from their portal as well.
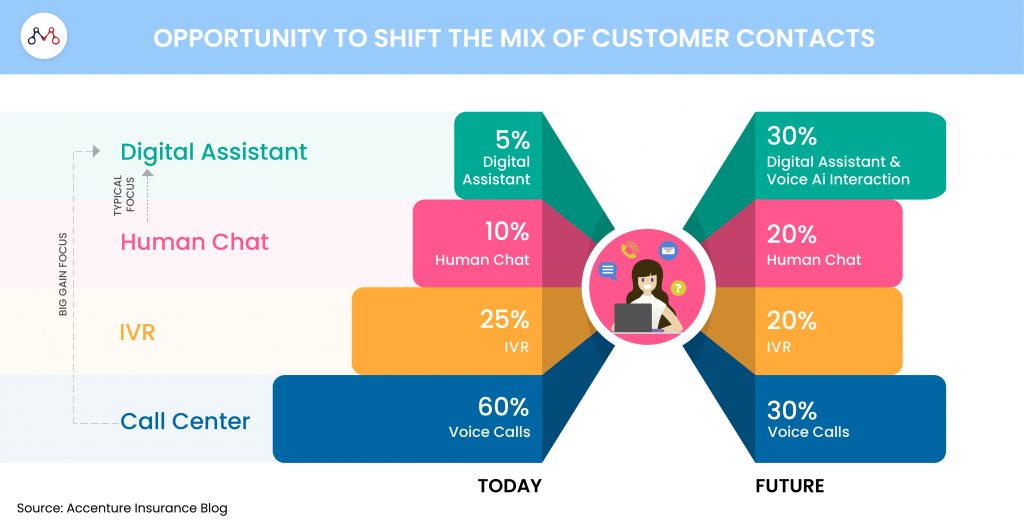
The biggest learnings for young insurtechs in this space from more mature markets, are about getting the basics right – having a single view of the customer, being able to launch rates and change pricing in real-time, offering customers a multichannel experience without requiring them to fill in the same information over and over again, and settling claims quickly without the need for multiple touchpoints.
Demand-driven models, built on sufficiently large data-sets will be instrumental in driving individual customisation at mass-scale for the sector at large.

Join our Webinar — AI for Data-driven Insurers: Challenges, Opportunities & the Way Forward hosted by our CEO, Parag Sharma as he addresses Insurance business leaders and decision-makers on April 14, 2020.
We help young insurtechs, build and scale AI-driven products and solutions for last-mile environments. Reach out to us on hello@mantralabsglobal.com, to learn more.
Knowledge thats worth delivered in your inbox